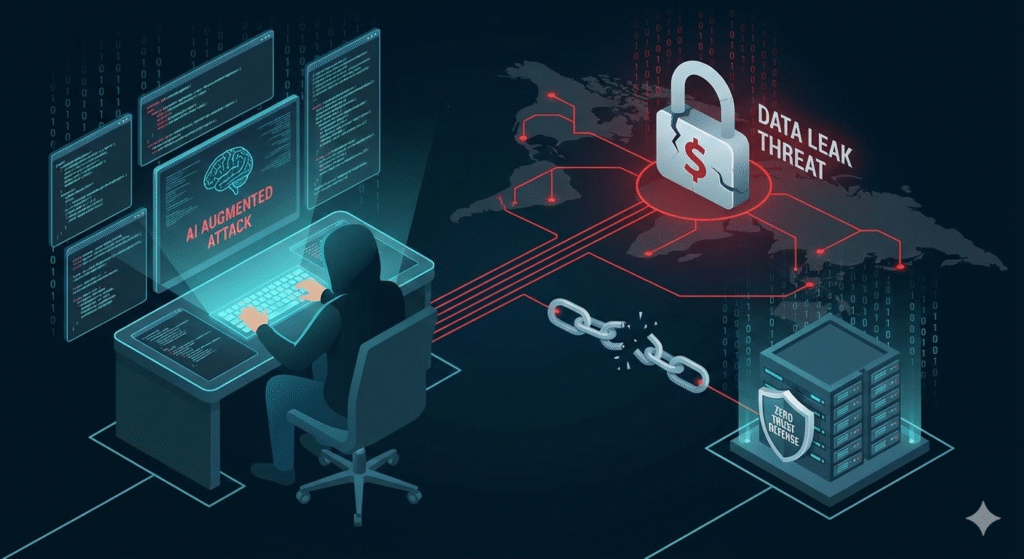
As we settle into 2026, the cybersecurity landscape has shifted dramatically. The image of the lone “hacker in a hoodie” punching code into a green screen is quaintly outdated. Today, cybercrime is a trillion-dollar global industry characterized by professionalism, specialization, and, most menacingly, the weaponization of artificial intelligence.
We have entered an era where the tools used to defend systems are the exact same tools used to break them. The battle is no longer man vs. machine; it is AI vs. AI, with humans caught in the crossfire.
Here is an overview of the current state of hacking, breaches, and the evolving threats defining 2026.
I. The Rise of the “AI-Augmented” Attacker
The most significant change in the last two years has been the democratization of sophisticated attack tools through generative AI.
Previously, crafting a convincing phishing email in impeccable business English required skill. Developing a zero-day exploit required deep technical knowledge. In 2026, “Agentic AI” models—the same type that book your flights—are being repurposed for malice.
- Hyper-Personalized Phishing: Attackers now use AI to scrape a target’s LinkedIn, recent posts, and company news to craft uniquely tailored spear-phishing emails at scale. These aren’t generic “reset your password” blasts; they are context-aware messages that mimic the tone of a CEO or a trusted vendor perfectly.
- Deepfake Social Engineering: The “CEO Fraud” call has evolved. Attackers are using real-time AI voice cloning to impersonate executives over the phone, authorizing urgent wire transfers. Video deepfakes are also being used to bypass biometric identity verification systems during onboarding processes.
- Automated Vulnerability Discovery: AI agents can now scan code faster than any human, identifying weaknesses in software and automatically generating exploit code before vendors even know a patch is needed.
II. Ransomware 3.0: Extortion Over Encryption
Ransomware remains a scourge, but the business model has changed. The days of simply encrypting files and demanding Bitcoin for a decryption key are fading.
In 2026, the primary tactic is “Double Extortion” (and sometimes triple).
- The Theft: Attackers quietly infiltrate a network and spend weeks exfiltrating sensitive data—customer records, intellectual property, internal emails.
- The Lock: Only after the data is stolen do they deploy encryption to cripple operations.
- The Threat: If the company refuses to pay the ransom because they have good backups, the attackers threaten to leak the stolen data publicly.
The leverage has shifted from operational downtime to reputational destruction and regulatory fines. Backups are no longer a “get out of jail free” card.
III. The “Harvest Now, Decrypt Later” Threat Looming
A quieter, more existential threat driving security policy in 2026 is the shadow of quantum computing.
While a fully capable quantum computer that can break today’s standard encryption (like RSA) doesn’t exist yet, nation-state actors are operating on a “Harvest Now, Decrypt Later” strategy. They are scooping up vast amounts of encrypted global data traffic today and storing it in massive data centers, waiting for the day—perhaps 5 to 10 years from now—when quantum technology matures enough to unlock it instantly.
This fear is driving the current, urgent migration to Post-Quantum Cryptography (PQC) standards in government and finance sectors.
IV. The Supply Chain as the Backdoor
Why spend months trying to hack a fortress like a major bank or tech giant when you can just hack the small, under-resourced company that provides their cafeteria software or HR tools?
Supply chain attacks remain the most effective way to compromise high-value targets. By inserting malicious code into a widely used software update or compromising a third-party vendor’s credentials, attackers gain trusted access to thousands of downstream organizations instantly. In the interconnected digital ecosystem of 2026, you are only as secure as your weakest vendor.
The New Defense Reality
The defense landscape in 2026 is defined by the realization that perimeter walls are insufficient. The prevailing philosophy is “Zero Trust”—assume the breach has already happened and verify every single request for access, regardless of where it comes from.
Furthermore, defense is now heavily reliant on AI-driven threat detection. Security Operations Centers (SOCs) are using AI models to analyze terabytes of network log data in real-time, looking for subtle behavioral anomalies that a human analyst would never spot.
We are in an arms race. As attacker AI gets smarter, defender AI must stay one step ahead. But amidst all this high-tech warfare, the most critical vulnerability remains the same as it was twenty years ago: the human being who clicks on the wrong link.